需求说明
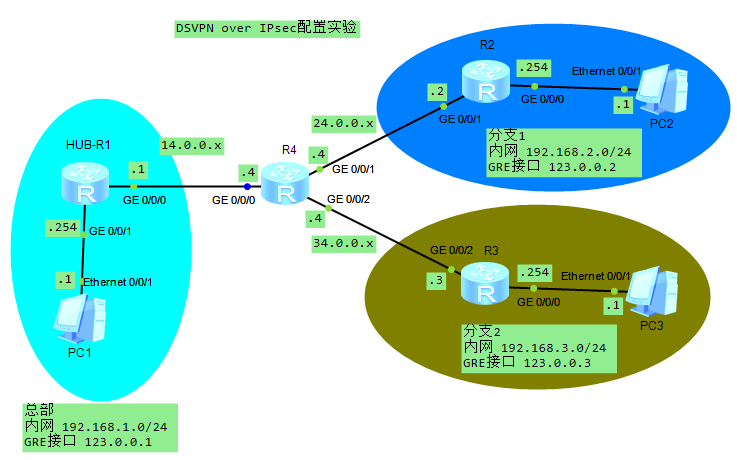
总部和2个分支办公室打通内网互联,分支间互访建立动态直连隧道,隧道采用IPsec加密并运行OSPF维护内部路由。
拓扑图
配置思路
采用GRE P2MP协议,配合IPsec加密,隧道内运行OSPF。
- 打通互联网R1-R2-R3-R4,配置设备和PC接口IP
- 配置总部和分支R1-R2-R3 GRE隧道接口,R2/R3开启nhrp向总部R1注册
- 配置总部和分支R1-R2-R3 OSPF并宣告内网和隧道接口IP
- 修改GRE隧道参数。启用nhrp动态多播支持,OSPF网络为广播并关闭分支DR选举
- 配置IPsec提议,IKE提议,IKE对等体,IPsec模板调用以上配置
- 关闭R1/R2/R3隧道接口,调用IPsec模板。启用HUB-R1隧道后再启用分支隧道接口
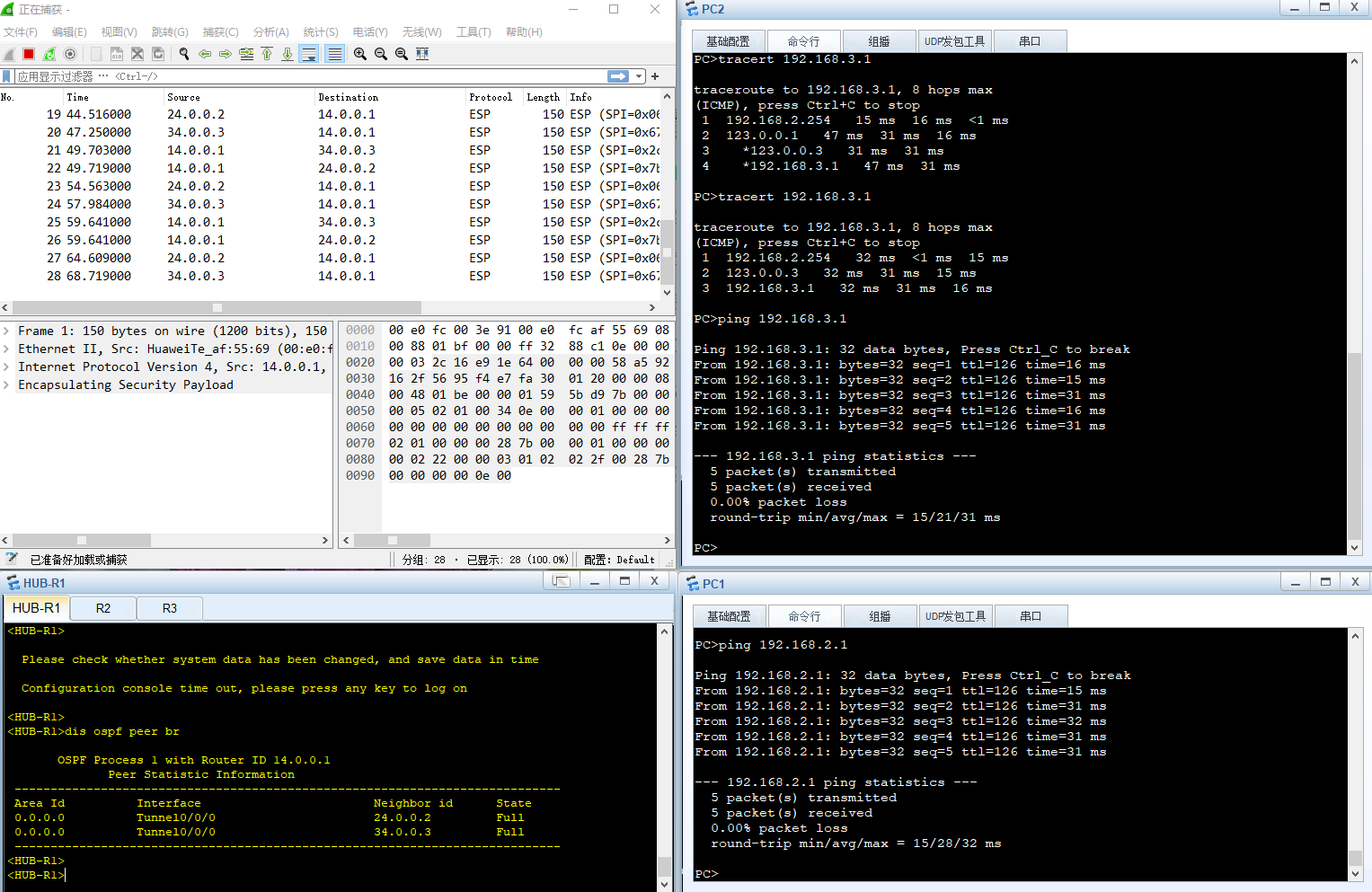
- 测试配置,检查OSPF邻居,总部ping分支1-2,分支1到分支2查看路由跟踪,抓包查看加密状态。
1.打通互联网R1-R2-R3-R4,配置设备和PC接口IP。PC1/PC2配置如图
#HUB-R1
sysn HUB-R1
int g0/0/0
ip addr 14.0.0.1 24
int g0/0/1
ip addr 192.168.1.254 24
ip route-static 0.0.0.0 0 14.0.0.4
#R2
sysn R2
int g0/0/0
ip addr 192.168.2.254 24
int g0/0/1
ip addr 24.0.0.2 24
ip route-static 0.0.0.0 0 24.0.0.4
#R3
sysn R3
int g0/0/0
ip addr 192.168.3.254 24
int g0/0/2
ip addr 34.0.0.3 24
ip route-static 0.0.0.0 0 34.0.0.4
#R4
sysn R4
int g0/0/0
ip addr 14.0.0.4 24
int g0/0/1
ip addr 24.0.0.4 24
int g0/0/2
ip addr 34.0.0.4 242.配置总部和分支R1-R2-R3 GRE隧道接口,R2/R3开启nhrp向总部R1注册
#HUB-R1
int tun0/0/0
ip addr 123.0.0.1 24
tunnel-protocol gre p2mp
source 14.0.0.1
#R2
int tun0/0/0
ip address 123.0.0.2 24
tunnel-protocol gre p2mp
source 24.0.0.2
nhrp entry 123.0.0.1 14.0.0.1 register
#R3
int tun0/0/0
ip address 123.0.0.3 24
tunnel-protocol gre p2mp
source 34.0.0.3
nhrp entry 123.0.0.1 14.0.0.1 register3.配置总部和分支R1-R2-R3 OSPF并宣告内网和隧道接口IP
#HUB-R1
ospf 1 router-id 14.0.0.1
area 0
network 123.0.0.1 0.0.0.0
network 192.168.1.0 0.0.0.255
#R2
ospf 1 router-id 24.0.0.2
area 0
network 123.0.0.2 0.0.0.0
network 192.168.2.0 0.0.0.255
#R3
ospf 1 router-id 34.0.0.3
area 0
network 123.0.0.3 0.0.0.0
network 192.168.3.0 0.0.0.2554.修改GRE隧道参数。启用nhrp动态多播支持,OSPF网络为广播并关闭分支DR选举
#HUB-R1/R2/R3
int tun0/0/0
ospf network-type broadcast
nhrp entry multicast dynamic
#R1/R2
int tun0/0/0
ospf dr-priority 05.配置IPsec提议,IKE提议,IKE对等体,IPsec模板调用以上配置。(为区分ike对等体,在分支R2/R3配置ike peer hub v2,总部R1配置ike peer spoke v2)
#HUB-R1/R2/R3
ipsec proposal p1
encapsulation-mode transport
esp authentication-algorithm sha2-512
esp encryption-algorithm aes-256
ike proposal 1
encryption-algorithm aes-cbc-256
dh group14
authentication-algorithm aes-xcbc-mac-96
ike peer spoke v2
pre-shared-key cipher huawei
ike-proposal 1
ipsec profile s1
ike-peer spoke
proposal p16.关闭R1/2/3隧道接口,调用IPsec模板。启用HUB-R1隧道后再启用分支隧道接口
#HUB-R1/R2/R3
int tun0/0/0
shut
ipsec profile s1
#HUB-R1
int tun0/0/0
undo shut
#R2/R3
int tun0/0/0
undo shut7.测试配置,检查OSPF邻居,总部PC ping分支1,分支1 PC2到分支2 PC3查看路由跟踪(第一次经过了总部转发,第二次就走正常分支间直连隧道了),抓包查看加密状态。达到预期效果。